Due to the recent data breach through GoDaddy, some clients using WordPress may have had their admin password changed to prevent a third party from accessing your site.
All clients using this product were notified via email of the potential for their email address to have been viewed and the potential for a third party to access their website.
As of this posting, no clients have affected from this potential threat. Further threats may be through email phishing, where you may receive an email baiting you to click links and enter credentials. Never click links in emails from an unconfirmed source.
If you have any questions or would like to discuss your account, please give me a call directly.
519-319-0875
Press release from GoDaddy:
On November 17, 2021, we discovered unauthorized third-party access to our Managed WordPress hosting environment. Here is the background on what happened and the steps we took, and are taking, in response:
We identified suspicious activity in our Managed WordPress hosting environment and immediately began an investigation with the help of an IT forensics firm and contacted law enforcement. Using a compromised password, an unauthorized third party accessed the provisioning system in our legacy code base for Managed WordPress.
Upon identifying this incident, we immediately blocked the unauthorized third party from our system. Our investigation is ongoing, but we have determined that, beginning on September 6, 2021, the unauthorized third party used the vulnerability to gain access to the following customer information:
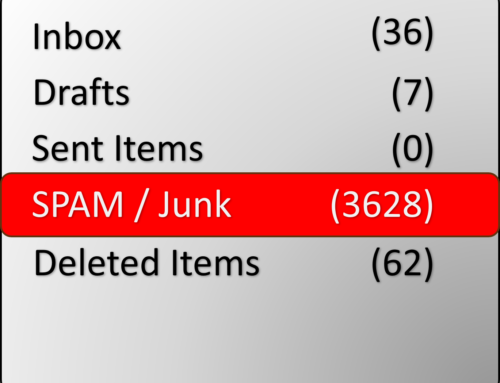
- Up to 1.2 million active and inactive Managed WordPress customers had their email address and customer number exposed. The exposure of email addresses presents risk of phishing attacks.
- The original WordPress Admin password that was set at the time of provisioning was exposed. If those credentials were still in use, we reset those passwords.
- For active customers, sFTP and database usernames and passwords were exposed. We reset both passwords.
- For a subset of active customers, the SSL private key was exposed. We are in the process of issuing and installing new certificates for those customers.
Our investigation is ongoing and we are contacting all impacted customers directly with specific details. Customers can also contact us via our help center (https://www.godaddy.com/help) which includes phone numbers based on country.
We are sincerely sorry for this incident and the concern it causes for our customers. We, GoDaddy leadership and employees, take our responsibility to protect our customers’ data very seriously and never want to let them down. We will learn from this incident and are already taking steps to strengthen our provisioning system with additional layers of protection.
Demetrius Comes
Chief Information Security Officer
Source: US Government